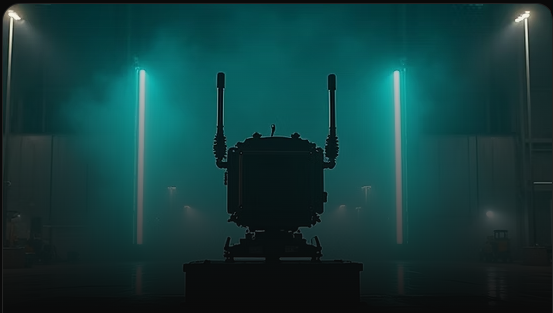
JDY 600 Overview
Engineered for Modern Aerial Threats
JDY-600 is a fixed drone sector jamming system designed to deliver targeted electronic interference within defined airspace sectors. Engineered for permanent installations, it effectively disrupts drone communication and navigation signals, providing reliable protection for critical infrastructure, defense facilities, and high-security zones against unauthorized UAV intrusions.
System Capabilities
Core Performance
Advanced technological capabilities defining the JDY-600’s sector-based jamming advantage.
Drone Detection
Advanced sensors detect unauthorized aerial threats
Signal Disruption
Precision interference disrupts hostile control signals
Remote Monitoring
Real-time command hub integration alerts
Airspace Protection
Comprehensive perimeter security and defense
Defining Capabilities
Key Features
Engineered for mission-critical performance in the most demanding environments
Multi-Band Interference
Disrupts drones across multiple frequency bands.
Our system employs advanced multi-band interference technology to effectively neutralize a wide spectrum of drone communication and navigation signals, ensuring comprehensive airspace denial.
Long-Range Coverage
Extensive detection and mitigation range. Achieve superior situational awareness with our long-range detection capabilities, extending your protective perimeter far beyond immediate threats and providing ample reaction time.
Rugged Industrial Design
Built for extreme environments and durability. Engineered to withstand the harshest operational conditions, our system features a rugged, industrial-grade design ensuring reliability and performance in any climate or terrain.
Rapid Deployment
Quick and efficient setup for immediate protection. Designed for operational agility, our counter-drone system can be rapidly deployed and activated, providing immediate protective measures against evolving aerial threats with minimal setup time.
Continuous Operation
Uninterrupted protection, 24/7 monitoring. Ensure constant vigilance with a system built for continuous, 24/7 operation. Our robust architecture guarantees uninterrupted performance and persistent airspace security.
Secure & Controlled Usage
Authorized operation with robust security protocols. Operate with confidence. Our system incorporates advanced security protocols and controlled access mechanisms, ensuring usage is strictly authorized and compliant with regulatory standards.
System Workflow
How It Works
A streamlined defense protocol designed for rapid response and maximum effectiveness
Detect Unauthorized Drones
Our advanced sensor array continuously scans the designated airspace, utilizing multi-spectral detection to identify and classify all aerial objects, distinguishing between authorized and unauthorized drones with high precision.
Locate the Drone and Operator
Using advanced signal analysis and direction-finding algorithms, JDY-600 supports real-time threat localization and airspace awareness, enabling operators to assess drone activity and coordinate effective sector-based jamming responses.
Neutralize the Threat Safely
Once a threat is confirmed, JDY-600 activates sector-focused electronic jamming to disrupt drone communication and navigation signals, preventing mission execution and denying access to protected airspace while minimizing unintended impact.
Monitor, Log, and Respond
All jamming operations and system activities are presented through a secure monitoring interface. Operators receive real-time alerts, event logs, and system status updates to support coordinated response and post-incident analysis.
Deployment Scenarios
Mission Applications
Proven protection across critical sectors and high-security environments
Airports & Aviation
Protecting airport perimeters and flight paths from unauthorized drone incursions to ensure passenger safety and operational continuity.
- Key Benefits: Enhanced air traffic safety, prevention of flight disruptions, compliance with aviation regulations, rapid threat neutralization.
- Challenges Addressed: Drone-related flight delays/cancellations, potential for collisions with aircraft, security breaches, unauthorized surveillance.

Critical Infrastructure Protection
Safeguarding vital national assets such as power plants, water treatment facilities, and communication hubs from aerial threats and espionage.
- Key Benefits: Uninterrupted operation of essential services, protection against sabotage, prevention of data exfiltration, enhanced physical security.
- Challenges Addressed: Industrial espionage, physical attacks via drones, unauthorized data collection, disruption of critical services.

Border & Coastal Security
Monitoring and securing national borders and coastal regions against illegal crossings, smuggling, and reconnaissance by hostile entities using drones.
- Key Benefits: Improved border surveillance, interdiction of illicit activities, enhanced national security, rapid response to aerial threats.
- Challenges Addressed: Cross-border smuggling, illegal immigration, reconnaissance by adversarial forces, difficulty in monitoring vast areas.

Public Event Security
Ensuring the safety and security of large public gatherings, concerts, and sporting events by neutralizing unauthorized drones that pose risks to attendees.
- Key Benefits: Enhanced public safety, prevention of security incidents, protection of VIPs, compliance with event security protocols.
- Challenges Addressed: Terrorist threats, unauthorized filming/surveillance, disruption of events, potential for dropping dangerous payloads.

Military & Defense Sites
Providing robust counter-drone capabilities for military bases, training grounds, and forward operating positions to protect personnel and sensitive assets.
- Key Benefits: Protection of classified information, prevention of reconnaissance, enhanced force protection, operational readiness.
- Challenges Addressed: Adversarial intelligence gathering, direct attacks, unauthorized surveillance of sensitive operations, maintaining air superiority.
Authorized Use Only
Designed for professional defense, government, and authorized security personnel.
Global Deployment
Suitable for fixed, mobile, and temporary deployments worldwide.
Enterprise Integration
Seamlessly integrates with existing C2 systems and security infrastructure.
Important Notice
This counter-drone defense system is a controlled technology designed for authorized security and defense applications only. Deployment requires proper licensing, regulatory approval, and trained personnel. Unauthorized use, sale, or export is strictly prohibited and may result in severe legal consequences. All operators must comply with local, national, and international laws governing radio frequency interference and airspace security.







Reviews
There are no reviews yet.